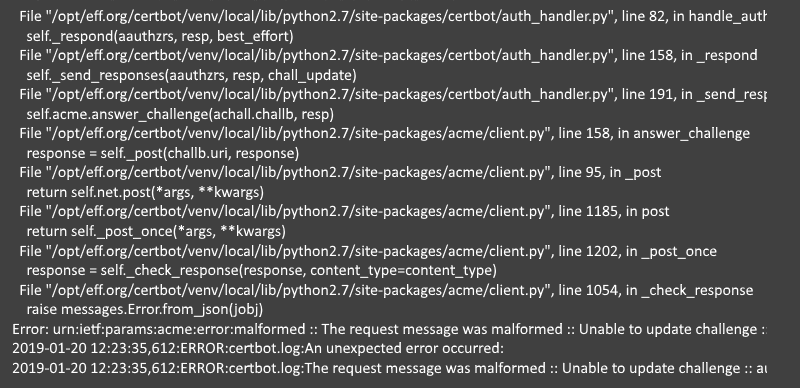
The mantra of cyber security experts is that you shouldn’t make plans thinking if you are hacked, but plan for recovery when you are hacked. Sure, according to studies and statistics it is practically inevitable that especially small … Read the story...
The most successful cyber attack method is triggered by victims themselves
The nasty thing with social engineering is that the victim falls for a scam, and ultimately helps cyber criminals to achieve their goal. Typically they want to break into a large computer system or simply access the victim’s bank account. … Read the story...
The problem with privacy: ideas and real life behavior don’t match
Scientists have researched for years the mismatch of results originating from interviews and surveys, and the actual behavior of people. Something tends to be wrong with the results, although respondents feel they have given accurate answers. This phenomenon is surprisingly … Read the story...
Is social media on a trajectory to become an old-media like gatekeeper?
What a joy it was to realize that it really was possible to publish anything we wanted on a blog, or comment on other people’s blogs. Sharing witty remarks on Twitter and holiday beach photos on Facebook was better than … Read the story...
What small businesses and homes can learn from the Twitter whistleblower
One of the last big decisions Jack Dorsey made before handing over Twitter’s CEO responsibilities to Parag Agrawal was to hire a cybersecurity expert to fix the numerous security problems the company has. Peiter “Mudge” Zatko accepted Dorsey’s offer, and … Read the story...
Have you misunderstood Linux?
Linux is an excellent piece of software, but what exactly is it? Your mobile phone may run Linux if it is powered by Android, the most powerful cloud servers on the internet are powered by Linux, your security camera may … Read the story...
Inside Facebook: what makes the Zuckerberg machine tick
Facebook is such a powerful global enterprise that its founder and CEO Mark Zuckerberg and other leaders haven’t always understood its might. The social media service has been exploited to rig elections, to develop terrorist and hate communities, and spread … Read the story...
Phishing is not rocket science: here are samples that draw clicks
Cyber security company Kaspersky has collected information on types of email messages that convince receivers to click dangerous links. The company has created a product that allows organizations to simulate attacks, phishing attempts and other threats. Simulation campaigns are targeted … Read the story...
Privacy paradox and five more data related megatrends
Collecting internet users’ data for trading it for profit is such a big business that it is not going to die anytime soon, even though people and governments across the world are getting increasingly worried about this shady practice. EU’s … Read the story...
The one and only cybersecurity rule for small businesses
If you haven’t been hacked yet, sooner or later you will be. This uncomfortable realization has been stuck in my head ever since I read Nicole Perlroth’s book This Is How They Tell Me the World Ends: The Cyberweapons Arms … Read the story...