It is only a matter of time when one of the web services you are using gets hacked. A common objective for data thieves is to steal databases that include user data, such as names, passwords, phone numbers, birth dates, addresses, and credit card numbers. The data is used for two purposes: it has intrinsic value, and the user name-password combinations are used for signing in to other popular cloud services. Even if your user name-password combination ends up at wrong hands, it can’t be used at all – if you have activated a security measure known as two-factor authentication.
Options for two-factor authentication
Two-factor authentication is an additional security measure for signing in to online services. The traditional method of using a user name-password combination alone is not considered safe enough anymore, even if you have a strong, unique password.
Two-factor authentication adds another level of security by requiring a second code. Here is how it works: you login to a service with your username and password, and after they have been verified, the service asks for an additional code. This code is what makes the method secure. Even if thieves have your user name and password, they can’t login because they don’t have your additional code.
There are a number of ways to generate the second level secure code. The common methods are:
- An application on a phone or tablet that can generate a code that matches with the code the service has.
- A text message (SMS) that the online service sends to your phone.
- A special USB stick that generates a code.
Purely from security standpoint, experts rank the dedicated USB stick as the safest, and the mobile application as the second safest choice. The mobile application method with Time based One Time Password is regarded as the best option when the balance between convenience and security is considered.
The step-by-step process to setup a reliable and secure two-factor authentication
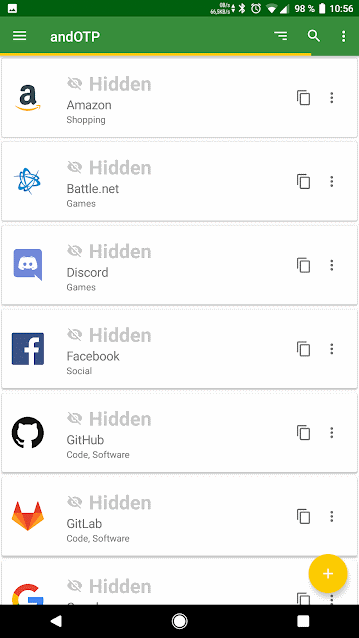
There are many mobile applications for Android devices and Apple devices that can be used for adding a secure login to a cloud service. The following step-by-step guide ia based on an Android app called andOTP. I tried many apps, and andOTP simply was the easiest to setup and use. Independent of which app you choose, the following process is roughly the same for all two-factor authentication apps.
On a computer, visit the online service whose login you want to secure
- Many cloud services, like Facebook, Amazon, Godaddy have two-factor authentication available as an option. Sign in to the service you want to secure.
- Go to your account settings. Find the option that lets you activate two-factor authentication.
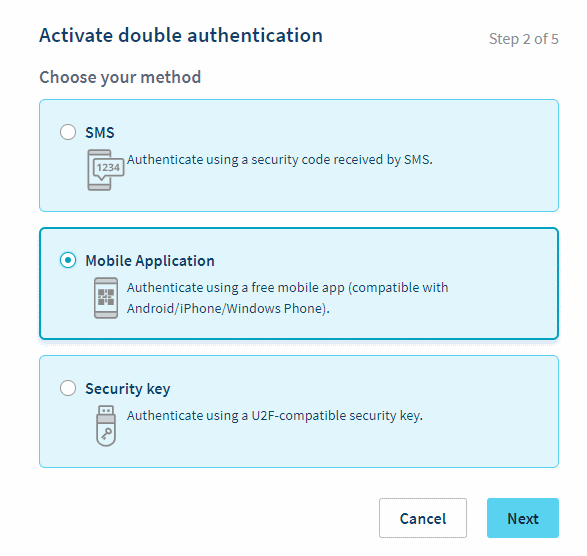
- If there are alternative methods available, choose Mobile App, OTP, or similar that requires an application on your phone or tablet.
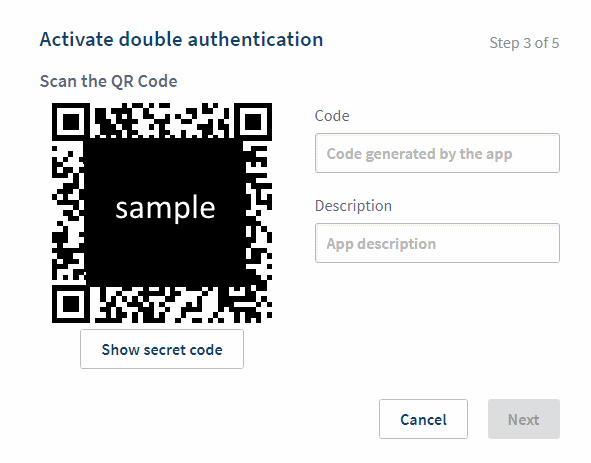
- Next, the services usually show an QR code on the screen. It is time proceed with the setup on a phone or tablet.
Pick up your phone or tablet you will use for secure authentication
- Download andOTP app from Google Play Store to your phone or tablet (or another app if you want to use something else).
- When you start the andOTP app, it will guide you through a setup process.
a. Choose Password/PIN for Database Encryption.
b. Authentication: choose Password, and enter the new password into the required field (twice). You will use this password to open the andOTP app in the future. - Once the setup is ready, an empty list of sites is displayed. To add a new secure login to andOTP, push the yellow plus-button. Then, the easiest way to proceed is to choose Scan QR Code.
- Point the phone camera to the QR Code that is waiting on the computer screen. Wait a moment for the app to read the information in the image. Once the app has interpreted the data, the web site information is displayed on the phone as a new entry appears on the andOTP screen.
- A six-digit code is displayed for the web service you are setting up. View the yellow bar at the top of the screen. Before it reaches the last third of the bar width, enter the six-digit code into the computer (into the Code, OTP or similar field displayed next to the QR Code).
- Some web services provide you with Emergency Codes that can be used if everything else fails, or you lose your mobile device. Save the codes carefully (I have already needed mine once).
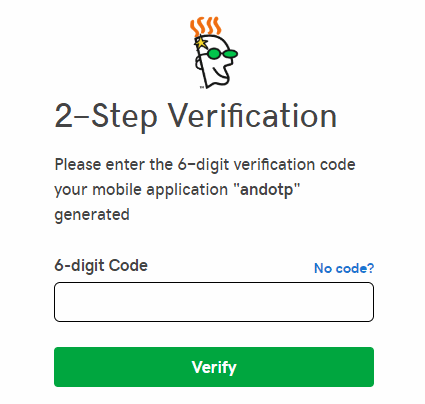
- Now, you should be ready to login securely to the service. It is a good idea to test that it works. On your computer, log out from the service that was just secured. Sign in again. The service should ask for an additional code after your user name and password. On your phone or tablet, open andOTP and use the six-digit code displayed for the web service entry to login to the site.
A few terms commonly used in security applications
- 2FA – Two-Factor Authentication. Also: Two-step verification, double-authentication. Technical details may vary, but the purpose is to secure login to a service by adding a second level authentication that relies on a device the user has.
- OTP – One-Time Password.
- TOTP – Time-based One-time Password.
- HOTP – HMAC-Based One-Time Password.
- QR code – a black and white square with hidden information a camera can read. See the image below for an example.
andOTP is being developed by Jakob Nixdorf who welcomes contributors to join the project. The application can be reviewed at Github.

The next web has an article for activating 2fa for PC gaming services
https://thenextweb.com/gaming/2019/02/19/two-factor-authentication-pc-gaming/amp/#click=https://t.co/f5xNz1RWBY
I believe everything said made a lot of sense. However, what about this?
suppose you were to create a killer title? I mean, I don’t wish to tell you how to run your blog, but suppose you added a title that grabbed folk’s attention? I
mean How to activate secure two-factor authentication for online services | | Andalys is
kinda boring. You could peek at Yahoo’s front page and watch how they create news titles to get viewers to click.
You might add a related video or a picture or two to get
readers interested about everything’ve written. In my opinion, it might make your posts a little livelier.
Hello, just wanted to say, I liked this blog post.
It was practical. Keep on posting!
Thanks for sharing your thoughts about 2fa.
Regards
Cool blog! Is your theme custom made or did
you download it from somewhere? A design like yours with
a few simple tweeks would really make my blog shine. Please
let me know where you got your theme. Appreciate it