Open source software products are often regarded safer and less vulnerable to malicious hacking than propriety software. The principle of showing the actual program code to the world and allowing other people and organizations to run the software is a valid method to discover potential problems. It is always a human who has written the code, however, and we all make mistakes.
Whitesource, an open source license management service, has put together a report that points out the scale of vulnerabilities in open source.
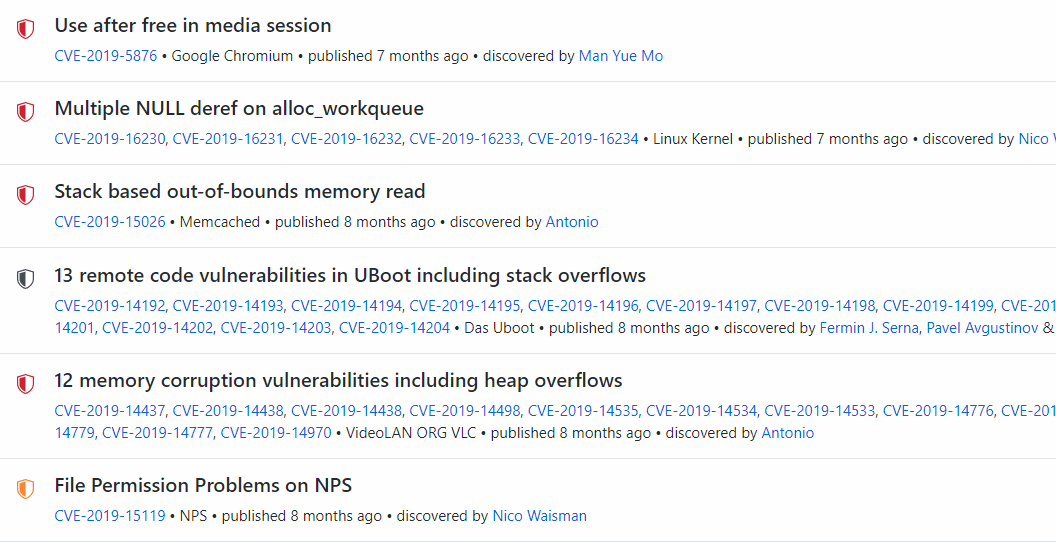
In March 2020, new reported vulnerabilities in open source software increased about 13% from February 2020. The total was 750 new reported cases in March according to the Whitesource report. While the number of discovered problems is not high, this is the amount of new vulnerabilities reported every month. Even with the 13% growth rate, it’ll soon be considerably high.
Popular open source software management service Github hosts more than 100 million project repositories. No one knows how many software projects are developed on other services and on individual computers. In this perspective, the number of monthly discovered vulnerabilities is low, perhaps even too low.
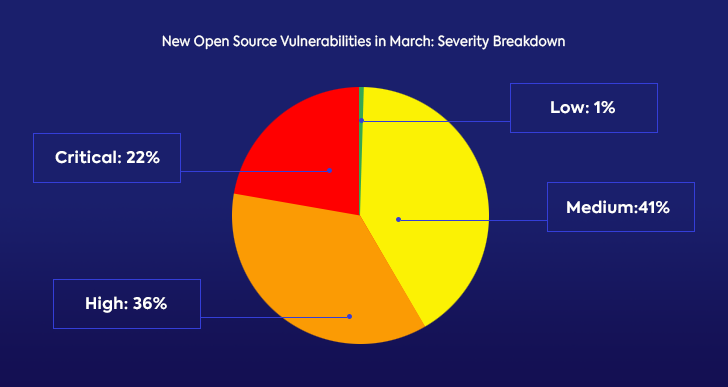
The risk evaluation for vulnerabilities has remained relatively constant: 22% are critical, 36% high, 41% medium and 1% low risk problems. It means that the majority (58%) of bugs are in high risk category.
Cross-site scripting is the most common problem. Categorised as CWE-79 (here is the detailed definition), it is about twice as common as the next two, CWE-200 and CWE-20, both related to interaction with users.
When the legendary computer company Sun introduced new programming language Java to the world more than 20 years ago, the key point that it is the secure tool for the internet era. Well, how about this: PHP, Java, Javascript and C are the four languages with most mentions in open source bug database. Probably this has something to do with the fact that they also happen to be the most used programming languages on the internet, but still.
Whitesource has compiled the monthly open source vulnerability report from NVD (National Vulnerability Database – a U.S. initiative, but features problem reports from other parts of the world, also from Github) and other sources.